You can connect to any type of API you have access to. We support different types of authentication that should meet most requirements.
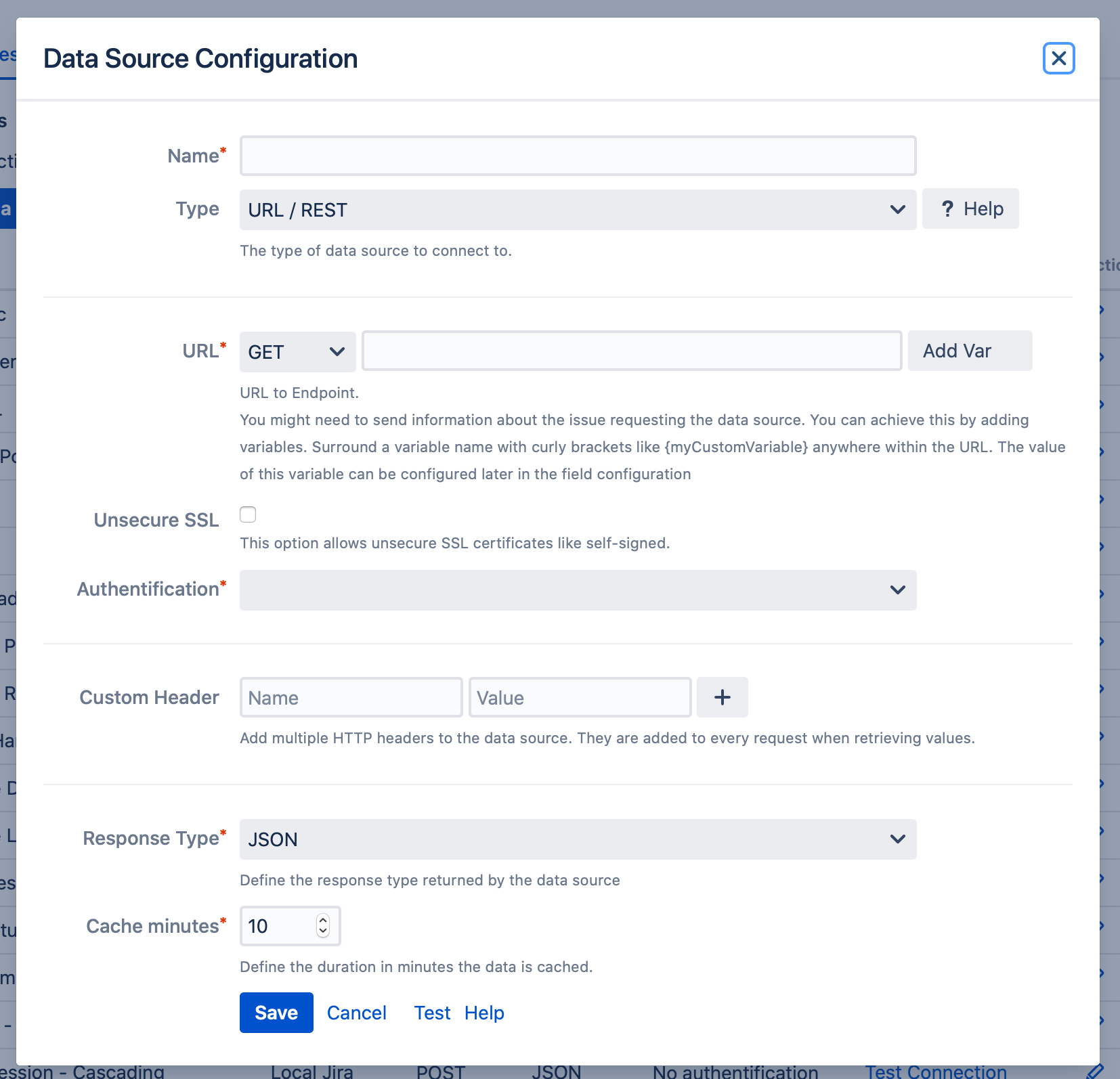
URL
Enter the URL of the endpoint you want to retrieve data from.
For example:
https://myApiUrl.com
If you add additional parameters to your URL, we suggest to URL encode the parameters. For that, you can use tools like https://www.urlencoder.org/.
While we try to encode problematic characters automatically, this can fail in some rare cases.
Method Selection: GET or POST
When connecting to an endpoint, you have the flexibility to use either the GET or POST method, depending on the specific requirements of the endpoint.
POST Method:
-
Content Type and Body: If you choose the POST method, you can define both the Content Type and the Post Body for the request.
-
Custom Header: When you select "Custom Header" for the Content Type, you must manually enter the value in the Custom Header section of the configuration below.
Variables
You may need to send information about the problem to request the data source. To do this, you can add variable names in curly brackets (like {myCustomVariable}) anywhere within the URL. The value of this variable can be customized in the field configuration later on.
Example:
https://myApiUrl.com?issueId={varIssueID}&key={issueKey}
Variables can also be used in the content of a POST body.
Authentication
In this section you can define the authentication method of the data source you want to connect with. Currently, the following methods are supported:
-
No authentication
-
Basic Auth (Basic HTTP Authentication)
-
Bearer Token
-
OAuth 2 (OAuth 2 )
-
Custom Auth Header (for API tokens or other header based authentication)
Custom Auth Header
Define a single header name and value that you need for authentication. The header value is separately encrypted and will never be displayed again after saving the data source.
Custom Headers
Define custom headers as needed to individualize the requests sent to the data source. These custom headers will be sent with each request. Enter the name and value of the header you want to add and click the + button to check and confirm it.
Don’t store secrets in this section. Please use the Custom Auth Header authentication instead
Response Type
Defines the response type returned by the data source. Choose either JSONor XML.
Ports
The following TCP ports are supported for connecting to your data source:
-
80
-
443
-
3128
-
4443
-
5867
-
7048
-
7063
-
8000
-
8001
-
8008
-
8077
-
8080
-
8089
-
8443
-
8444
-
9080
-
9998
-
37469
-
37470
-
48080
If the port you need is not on the list, feel free to contact our Support.
Security Recommendations 
For best practices when connecting to an external URL/REST data source, we recommend the following steps:
-
Choose a suitable authentication method: Use the most secure authentication method supported by the external data source. The recommended order of preference is OAuth 2, Bearer Token, Custom Auth Header, Basic Auth, and finally, No Authentication (only for non-sensitive data).
-
Use a dedicated user account: If the data source supports user accounts, create a dedicated user account with limited permissions for connecting to the external data source. Grant read-only access to the specific data required by the app.
-
Rotate passwords and tokens regularly: If using Basic Auth or Bearer Token, change the password or token every six months, or more frequently if required by your organization's security policies. For OAuth 2, ensure token expiration and refresh policies are properly configured.
-
Enable secure communication: If the external data source supports HTTPS, make sure this option is enabled to encrypt data transmitted between the app and the data source.
-
Monitor access and usage: Regularly review logs and reports from the external data source to identify suspicious activities, such as unauthorized access or data exfiltration.